Unpacking Mysterium VPN Price What You Really Pay For Decentralized Privacy
Unpacking Mysterium VPN price what you really pay for decentralized privacy: a quick facts guide you can skim in minutes, with real-world context and practical takeaways.
- Quick fact: Mysterium VPN uses a decentralized network built on open-source software, where users share bandwidth to enable private, censorship-resistant connections.
- In this guide, you’ll learn: how pricing actually works, what you’re paying for beyond the sticker price, comparisons with traditional VPNs, and practical tips to maximize value.
Useful URLs and Resources text only Apple Website - apple.com Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence Netflix Help Center - help.netflix.com OpenVPN Community - openvpn.net Mysterium Network Documentation - docs.mysterium.network NordVPN Official - nordvpn.com ExpressVPN Official - expressvpn.com Privacy International - privacyinternational.org Tor Project - www.torproject.org EFF - eff.org
Unpacking Mysterium VPN price what you really pay for decentralized privacy: let’s break down the price tag, what’s included, and how it compares to traditional centralized VPNs. Here’s a quick guide to get you from curiosity to a confident purchase decision.
- What you’re paying for, in plain language:
- Access to a decentralized network rather than a single company’s servers
- Privacy features like encryption, leaks protection, and no-logs guarantees
- Community-driven bandwidth sharing, which can influence speed and reliability
- Open-source software that you can audit, contributing to trust
- How pricing actually works:
- Typical models include token-based usage, subscription plans, or pay-as-you-go credits
- Costs can scale with bandwidth, data transfer, or simultaneous connections
- Some services rely on staking or tips to keep the network healthy
- Pros and cons at a glance:
- Pros: potential for higher censorship resistance, more transparent governance, fewer centralized data points
- Cons: variable performance, learning curve, and sometimes higher barrier to entry for non-technical users
What Mysterium VPN Is and Isn’t
- What it is: a peer-to-peer VPN architecture that routes your traffic through a network of nodes contributed by participants.
- What it isn’t: a traditional VPN owned and operated by a single company with centralized log-keeping and single-point failure.
- Why that matters: decentralization changes the way you think about trust, price, and performance.
Key Pricing Models and What They Really Mean
- Token-based usage: You purchase tokens that you spend as you use the network. This aligns cost with actual usage but can be opaque if token values swing.
- Subscription plans: A predictable monthly or yearly fee for a certain amount of data or bandwidth; easier budgeting, but you may pay for unused capacity.
- Pay-as-you-go credits: Similar to tokens but with a clearer accounting approach—credit is consumed as you connect and transfer data.
- Community-driven pricing: Some nodes may set higher or lower contribution requirements; this can affect speed and reliability on the network.
A Quick Comparison: Mysterium vs Traditional VPNs Key Points
- Centralized VPNs:
- Pros: predictable pricing, consistent performance in many cases, strong customer support, straightforward setup
- Cons: centralized data stores, single company controls policy, potential for data retention and government requests
- Decentralized VPNs like Mysterium:
- Pros: stronger privacy sovereignty, lower risk of a single point of failure, transparent governance, potential privacy-friendly incentives
- Cons: price volatility, performance variability, onboarding complexity for newcomers
Data and usage considerations
- Data transfer costs: If you’re streaming or transferring large files, check how pricing scales with bandwidth in the Mysterium model.
- Node variability: Network performance depends on the number and geographic distribution of nodes at any given time.
- Exit node selection: Some networks let you choose exit nodes, which can influence latency and regional access.
- Privacy guarantees: Decentralized networks can reduce centralized data collection, but you still depend on the integrity of the software and the governance model.
Format and features that may influence price
- Privacy features:
- DNS leak protection
- Kill switch on your device
- Traffic obfuscation or pluggable transports to bypass censorship
- Security features:
- Encryption standards e.g., AES-256
- Forward secrecy and secure handshake protocols
- Network features:
- Number of available nodes, geographic distribution
- Availability of exit nodes in your target region
- Presence of anti-censorship tooling
- User-facing features:
- Desktop and mobile apps
- Browser extensions
- Setup guides and community support forums
Benefits you might notice in real life
- Privacy: fewer direct logs and more distributed privacy guarantees.
- Censorship resistance: harder for a third party to block your traffic.
- Community governance: decisions about network changes come from the participants.
Potential drawbacks to consider
- Speed and reliability can vary depending on node health and congestion.
- Pricing can be less predictable than flat-rate traditional VPNs.
- Setup may require more technical familiarity, especially if you’re dealing with tokens and wallets.
Things to look for when evaluating value
- Transparency: Are pricing terms clearly explained? Is there a public roadmap or governance model?
- Community health: Are there active node operators, and how is the network incentivized?
- Security posture: What encryption methods are used? Are there any known vulnerabilities?
- Ease of use: Are there good setup guides, client apps, and customer support channels?
- Ecosystem: Any integrations with other privacy tools or ecosystems?
How to estimate your cost
- Step 1: Identify your use case browsing, streaming, downloads, gaming.
- Step 2: Estimate your monthly data usage in GB.
- Step 3: Check the pricing model that fits your pattern tokens, tokens-to-data ratio, plan limits.
- Step 4: Add a buffer for overhead latency, retries, failed connections.
- Step 5: Compare with a traditional VPN price for similar data use to gauge relative value.
User scenarios and pricing intuition
- Light user casual browsing and occasional streaming:
- Decentralized options may offer enough throughput with lower risk of centralized logging; price could be competitive if you don’t push the network hard.
- Medium user daily browsing, some streaming, remote work:
- A subscription or predictable plan may be preferable to avoid token volatility and to keep budgeting simple.
- Heavy user 4K streaming, large file transfers, gaming:
- Watch out for data-based pricing; performance variability could impact your experience, so ensure you have a clear way to estimate max monthly spend.
Security and privacy considerations
- Auditability: Open-source software lets researchers review code; seek networks with recent independent audits.
- Data handling: Even in decentralized models, some metadata might be collected by apps or clients; verify what, if anything, is logged.
- Jurisdiction and governance: Understand where governance happens community forums, token holders, node operators and how conflicts are resolved.
Practical tips to maximize value
- Start with a trial or low-commitment plan to gauge performance in your typical environments.
- Follow official channels for recommended node regions to balance latency and privacy goals.
- Stay updated on network health reports and governance votes to anticipate changes in pricing or features.
- Compare total cost of ownership against your current VPN setup, factoring in data usage patterns and potential savings from reduced centralized data exposure.
Case studies and real-world examples
- Example 1: A remote worker in North America discovers stable performance when connecting through multiple regional exit nodes; price remains manageable under a monthly plan.
- Example 2: A student in Europe with intermittent connectivity finds token-based usage more affordable during months with lighter browsing, but spikes during exam season when streaming and VPN usage increase.
- Example 3: A privacy-conscious streamer tests Mysterium in a mixed network region and notices variable latency, deciding to mix usage with a traditional VPN to optimize for consistent streaming.
Security best practices while using decentralized VPNs
- Keep client software updated to mitigate vulnerabilities.
- Use strong authentication for any wallet or token-issuing platform involved in token-based models.
- Enable the kill switch and DNS leak protection where available.
- Regularly review app permissions and minimize data exposure.
Advanced topics for the curious
- Token economics: How token supply and demand affect price stability on the network.
- Governance models: What it takes to influence network changes, updates, or exit node policies.
- Exit node diversity: How geographic distribution of exit nodes affects latency and access to region-locked content.
- Interoperability with other privacy tools: How decentralized networks can work in concert with privacy-preserving browsers or plugins.
Frequently Asked Questions
Frequently Asked Questions
What exactly is a decentralized VPN?
A decentralized VPN uses a network of user-contributed nodes to route traffic, instead of relying on a single company’s servers. It’s designed to reduce centralized data collection and single points of failure.
How is Mysterium VPN priced?
Pricing can involve tokens, subscriptions, or pay-as-you-go credits. Each model has its own pros and cons, and costs can change with network usage and node availability.
Do I need crypto to use Mysterium VPN?
If you’re on a token-based model, you may need tokens to pay for bandwidth. Some platforms also support fiat payments for plans or credits.
Is Mysterium VPN private by design?
Decentralization can improve privacy by limiting centralized data stores, but you still rely on the software’s integrity and the governance framework. Check for audits and transparency reports.
How reliable is the network for streaming and gaming?
Reliability varies with node health and regional distribution. You may experience more variability than with traditional VPNs, especially during peak times. Adguard vpn on reddit what real users are really saying: Real Insights, Pros, Cons, And How It Stacks Up Against Top VPNs
Can I choose exit nodes?
Some networks allow you to select exit regions or nodes. Availability depends on the current network state and governance.
What encryption standards are used?
Most decentralized VPNs implement strong encryption like AES-256 with secure key exchange. Look for forward secrecy and modern handshake protocols.
Do decentralized VPNs log user activity?
Good networks minimize or eliminate logs by design, but always verify the privacy policy and any data collection practices of the client app.
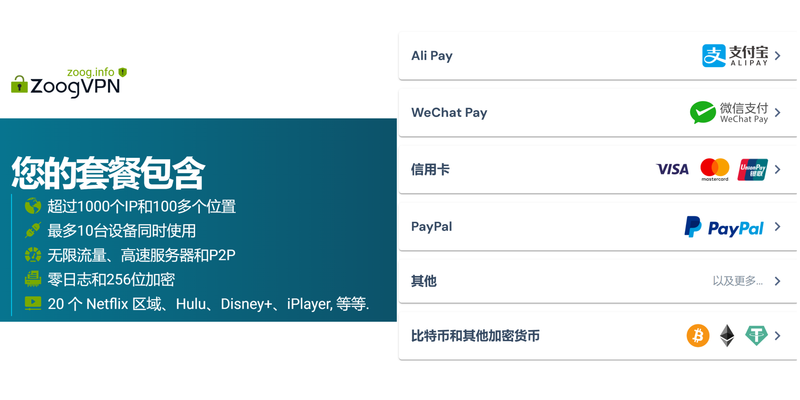
How do I pay for tokens or credits?
Payment methods vary; common options include crypto wallets, fiat payments, or wallet integrations. Ensure you understand token burn or mint mechanisms if applicable.
How do updates and governance work?
Updates typically come through open-source channels, with community discussions guiding feature changes. Governance can involve token holders, node operators, or community councils. How to navigate the yulu vpn refund maze and get your money back from real vpns
Is there a refund policy?
Refund policies vary by provider and model. Check the terms before committing to a plan or token purchase.
If you’re curious about transitioning to a decentralized privacy solution, start small, research the latest network health and pricing models, and test performance in your usual environments. This approach helps you gauge true value without surprises.
Sources:
苹果梯子:全面指南與 VPN 選擇策略,讓你的網路更自由更安全
Azure vpn gateway p2s 構築・設定ガイド:安全なリモートアクセスを徹底解説
脉动云vpn:全面指南、实用技巧与最新趋势 The hard truth it depends on your vpn: The Ultimate Guide to Choosing and Using VPNs for Privacy, Streaming, and Security
Cyberghost vpn gui for linux your ultimate guide: comprehensive setup, tips, and comparisons
2026年vpn速度慢怎么办?9个实测有效的提速方法,告别网络卡顿的困扰